US-Iran Cyber Warfare: The Hidden Digital Battlefield
Introduction: Understanding US-Iran Cyber Warfare in the Modern Digital Battlefield
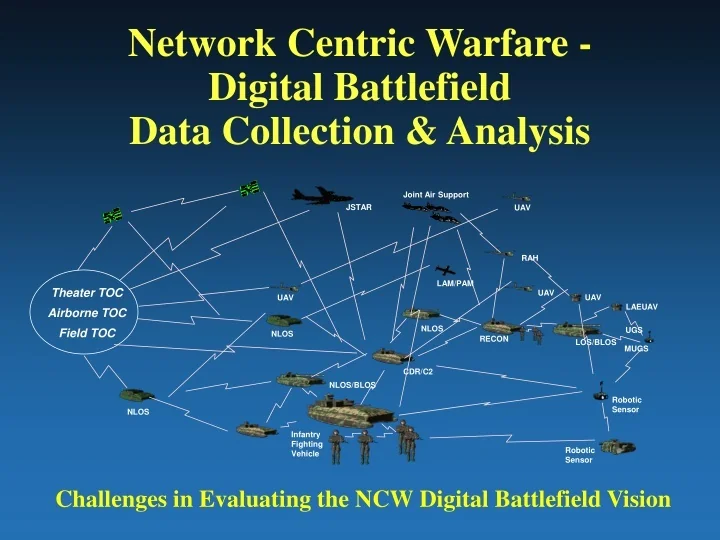
In recent years, US-Iran cyber warfare has become one of the most important yet least visible aspects of modern conflict. Unlike traditional wars fought with tanks, missiles, and soldiers, cyber warfare occurs in the shadows of the internet inside computer systems, communication networks, and digital infrastructure.
Today, governments around the world recognize that cyberspace is a new battlefield. As a result, both the United States and Iran have developed sophisticated cyber capabilities designed to disrupt enemy infrastructure, gather intelligence, and influence public perception. Consequently, the digital battlefield has become just as strategic as land, air, and sea operations.
While many people think of war as physical combat, cyber operations often occur before, during, and after military engagements. These attacks may target financial systems, military networks, energy infrastructure, or even social media platforms. Because of this, cyber warfare has fundamentally transformed how modern conflicts unfold.
If you want to learn more about the broader concept of cyber warfare, you can explore this detailed overview from the Council on Foreign Relations:
https://www.cfr.org/backgrounder/what-cyberwarfare
In this article, we will explore the rise of US-Iran cyber warfare, how cyber attacks are conducted, the technologies involved, and why digital conflict is shaping the future of global security.
The Rise of Cyber Warfare in Modern Conflicts

Why Cyber Warfare Has Become a Strategic Weapon
Over the past two decades, cyber warfare has evolved from isolated hacking incidents into a major strategic weapon used by nation-states. Unlike traditional warfare, cyber operations offer several advantages.
First, cyber attacks are relatively inexpensive compared to conventional weapons. Building a missile system costs billions of dollars, whereas launching a cyber operation may require only skilled programmers and specialized software.
Second, cyber attacks are often difficult to trace. Governments can hide their involvement through proxy groups, anonymous networks, or independent hacker collectives. Therefore, it becomes challenging for targeted countries to respond directly.
Third, cyber warfare allows attackers to damage critical infrastructure without physical destruction. For example, hackers can disrupt electricity grids, manipulate industrial systems, or disable communication networks.
Because of these advantages, countries like the United States, Iran, China, and Russia have invested heavily in cyber capabilities.
For a deeper explanation of how cyber attacks work in global conflicts, you can read this informative guide by the Cybersecurity & Infrastructure Security Agency:
https://www.cisa.gov/cybersecurity
The History of US-Iran Cyber Warfare
Early Digital Confrontations Between the US and Iran
The roots of US-Iran cyber warfare date back more than a decade. As geopolitical tensions increased, cyberspace became an alternative arena for strategic confrontation.
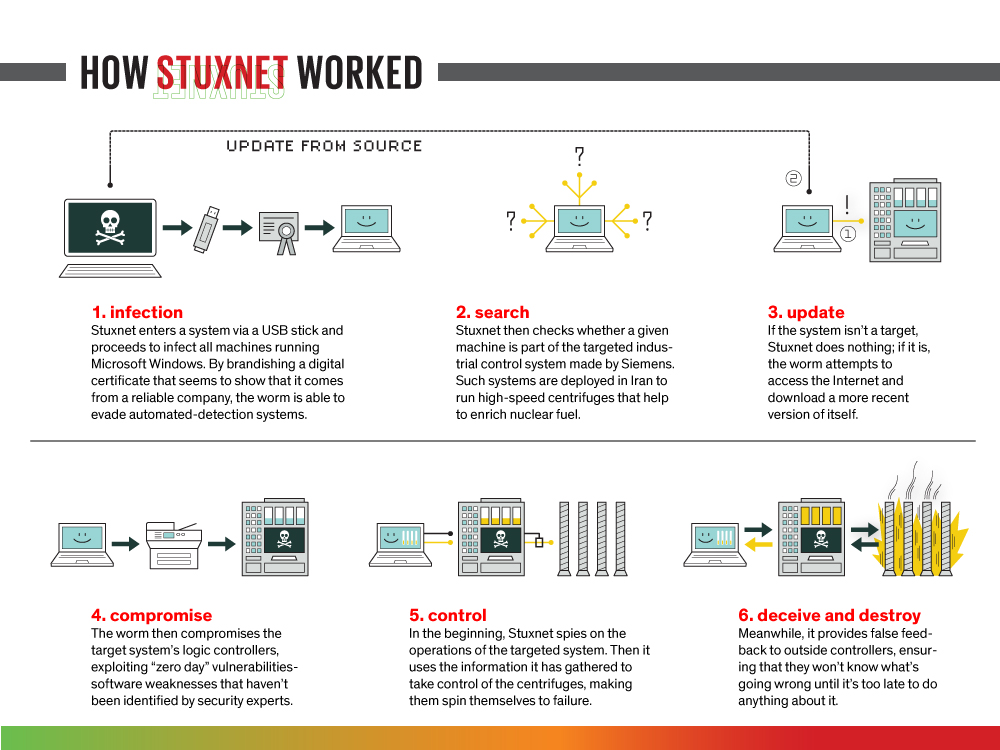
One of the most widely discussed cyber operations was the Stuxnet attack, discovered in 2010. This sophisticated computer worm targeted Iran’s nuclear enrichment facilities. The malware infiltrated industrial control systems and caused centrifuges to malfunction.
Although the operation was never officially confirmed, cybersecurity experts widely believe that the United States and its allies developed the Stuxnet malware. As a result, the incident demonstrated how cyber weapons could damage physical infrastructure.
However, Iran quickly began strengthening its own cyber capabilities. Soon afterward, Iranian cyber units and affiliated hacker groups launched attacks targeting banks, government agencies, and private companies.
Therefore, the digital rivalry between the two nations intensified significantly.
To understand the technical background of the Stuxnet cyber weapon, you can read this technical analysis:
https://www.wired.com/story/stuxnet-digital-weapon-history
Cyber Warfare Tactics Used in the US-Iran Digital Battlefield
1. Distributed Denial-of-Service (DDoS) Attacks
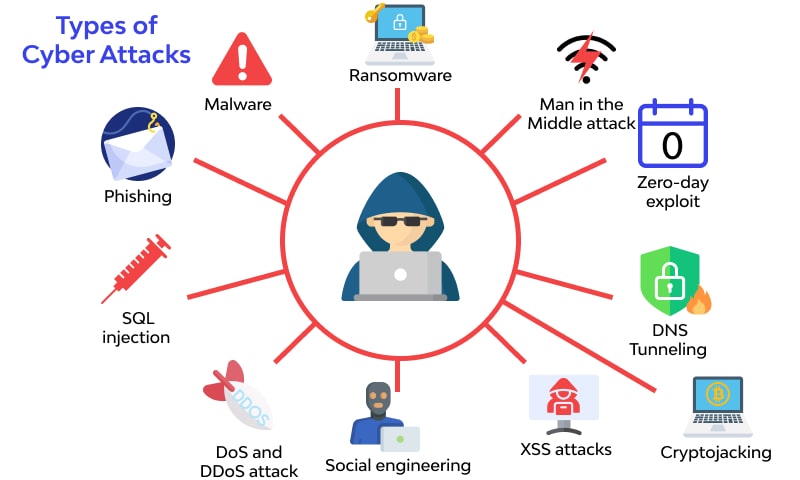
One of the most common techniques in US-Iran cyber warfare is the Distributed Denial-of-Service attack, commonly known as a DDoS attack.
In this method, hackers flood a target website or server with massive amounts of traffic. Consequently, the system becomes overwhelmed and stops functioning normally.
For example, attackers might use thousands of infected computers often called a botnet to send millions of requests to a website simultaneously. As a result, the website crashes or becomes inaccessible to users.

Although DDoS attacks rarely cause permanent damage, they can disrupt government services, financial institutions, or news platforms during critical moments.
2. Malware and Cyber Espionage
Another important tactic in the US-Iran cyber conflict involves the use of malware for espionage purposes.
Malware refers to malicious software designed to infiltrate computer systems. Once installed, it can:
- Steal sensitive data
- Monitor communications
- Record keystrokes
- Access confidential documents
In cyber espionage operations, attackers often remain hidden inside networks for months or even years. During that time, they quietly gather intelligence that could later be used for military or political advantages.
Because information is a powerful resource, cyber espionage has become a crucial component of modern warfare.
3. Critical Infrastructure Attacks
Perhaps the most dangerous element of US-Iran cyber warfare involves attacks on critical infrastructure systems.
Critical infrastructure includes essential services such as:
- Electricity grids
- Water treatment facilities
- Transportation systems
- Telecommunications networks
- Financial institutions
If hackers successfully disrupt these systems, the consequences could be severe. For instance, power outages or banking disruptions could affect millions of civilians.
Therefore, many governments now treat cyber infrastructure protection as a national security priority.
Cyber Warfare Technologies Powering the Digital Battlefield
Artificial Intelligence in Cyber Warfare
Artificial intelligence is rapidly transforming cyber warfare technology. AI-powered systems can detect vulnerabilities, analyze large datasets, and automate cyber attacks.
For example, AI algorithms can scan thousands of systems to identify weaknesses within seconds. Once vulnerabilities are found, automated tools can attempt to exploit them.

However, AI is also used for defensive purposes. Cybersecurity systems powered by machine learning can detect suspicious network behavior and respond instantly.
Consequently, the cyber battlefield has become a race between offensive AI tools and defensive cybersecurity systems.
Artificial intelligence is rapidly transforming cyber warfare technology. Modern AI systems can detect vulnerabilities and launch automated security responses. If you want to explore more about the fastest AI-powered storage technologies, read our guide onBest Portable SSDs for High-Speed External Storage in 2026.
Military Cyber Units and Digital Defense Systems
To strengthen their cyber capabilities, many countries have created specialized military cyber units.
These units are responsible for:
- Protecting government networks
- Conducting cyber intelligence operations
- Responding to cyber attacks
- Developing digital defense strategies
The United States, for example, established the U.S. Cyber Command, which coordinates cyber operations across military branches.
Meanwhile, Iran has also expanded its cyber divisions within the Revolutionary Guard and other national security organizations.
Therefore, the competition in cyberspace continues to intensify.
The Role of Hacktivist Groups in US-Iran Cyber Warfare
Independent Hackers and Proxy Cyber Operations
Interestingly, not all cyber attacks in the US-Iran cyber warfare landscape come directly from governments. Many operations involve independent hacker groups or politically motivated activists known as hacktivists.
These groups may support one side of a conflict and conduct cyber attacks independently. In some cases, governments may quietly encourage or tolerate these activities.
Hacktivist operations often include:
- Website defacements
- Data leaks
- Social media account hijacking
- Propaganda campaigns
Because these groups operate outside formal military structures, their actions can complicate attribution and diplomatic responses.
Information Warfare and Online Propaganda
Social Media as a Digital Battlefield
Beyond direct cyber attacks, information warfare has become another crucial element of modern digital conflict.
In the context of US-Iran cyber warfare, social media platforms play a significant role in shaping narratives and influencing public opinion.
Governments and affiliated groups may use online platforms to:
- Spread propaganda
- Amplify political messages
- Influence foreign audiences
- Create misinformation campaigns
For example, coordinated networks of fake accounts often called bot accounts can rapidly spread messages across platforms like X, Facebook, and Telegram.
Therefore, the digital battlefield extends beyond technical systems into the realm of information and perception.
Cyber Defense Strategies Against Digital Warfare
Protecting National Infrastructure from Cyber Attacks
As cyber threats increase, countries are developing stronger cyber defense strategies.
These strategies often include several key elements.
First, governments invest heavily in cybersecurity infrastructure. This includes firewalls, threat detection systems, and network monitoring tools.
Second, organizations conduct cybersecurity training programs to educate employees about phishing attacks and other common threats.
Third, governments collaborate with private technology companies to share threat intelligence and improve defensive capabilities.
Because many cyber attacks target private companies, public-private partnerships have become essential for national cybersecurity.
International Cooperation in Cybersecurity
Although cyber warfare is competitive, countries sometimes cooperate to strengthen global cybersecurity.
International organizations and cybersecurity alliances work to:
- Share threat intelligence
- Develop cybersecurity standards
- Coordinate responses to large cyber incidents
However, political tensions can limit cooperation, especially in conflicts involving major geopolitical rivals.
Nevertheless, cybersecurity experts agree that global cooperation is necessary to prevent large-scale digital disasters.
The Future of US-Iran Cyber Warfare
Emerging Technologies in the Cyber Battlefield
Looking ahead, US-Iran cyber warfare is likely to become even more sophisticated as new technologies emerge.
Some of the most important future trends include:
Artificial intelligence cyber weapons
AI systems may automate cyber attacks and identify vulnerabilities faster than human hackers.
Quantum computing
Quantum technology could potentially break traditional encryption systems, making cybersecurity even more challenging.
Autonomous cyber defense systems
Future cybersecurity tools may automatically detect and neutralize threats without human intervention.
Because technology evolves rapidly, the cyber battlefield will continue to change.
Why Cyber Warfare Will Shape Future Conflicts
Ultimately, cyber warfare offers governments a powerful tool that sits somewhere between diplomacy and traditional warfare.
Unlike missiles or airstrikes, cyber attacks can achieve strategic objectives without immediate physical destruction. At the same time, they remain difficult to detect and attribute.
Therefore, many experts believe that cyber warfare will play a central role in future geopolitical conflicts.
As tensions between global powers continue, the digital battlefield may become the first front line of international conflict.
Frequently Asked Questions (FAQs) About US-Iran Cyber Warfare
1. What is US-Iran cyber warfare?
To begin with, US-Iran cyber warfare refers to digital conflicts between the United States and Iran that take place in cyberspace rather than on traditional battlefields. Instead of using physical weapons, both sides may rely on cyber tools such as hacking, malware, data breaches, and digital surveillance.
In many cases, these cyber operations are used to gather intelligence, disrupt critical infrastructure, or influence political narratives online. Therefore, cyber warfare has become a strategic tool that allows nations to compete without direct military confrontation.
2. Why is cyber warfare important in modern conflicts?
In today’s highly connected world, almost every sector depends on digital infrastructure. As a result, cyber warfare has become extremely important because it can target communication systems, financial networks, energy grids, and government databases.
Moreover, cyber attacks are often less expensive and harder to trace compared to traditional military actions. Consequently, many governments consider cyber operations a powerful tool for achieving strategic objectives while avoiding large-scale physical warfare.
3. What are the common cyber attack methods used in the US-Iran cyber conflict?
Several cyber attack techniques are commonly used in the US-Iran digital battlefield. These include:
- Distributed Denial-of-Service (DDoS) attacks, which overwhelm websites with traffic.
- Malware attacks, where malicious software infiltrates computer systems.
- Cyber espionage, which involves stealing sensitive data or intelligence.
- Phishing campaigns, designed to trick users into revealing confidential information.
In addition, attackers may attempt to access industrial control systems that manage infrastructure such as power plants and transportation networks.
4. Has cyber warfare ever caused real-world damage?
Yes, cyber warfare can have serious real-world consequences. For example, cyber attacks targeting industrial systems can disrupt physical equipment or critical services.
Furthermore, cyber operations may affect banking systems, electricity grids, or communication networks, potentially impacting millions of people. Because of this, cybersecurity experts warn that cyber warfare could become one of the most disruptive forms of conflict in the future.
5. How do countries defend themselves from cyber warfare?
To protect against cyber threats, governments implement several cybersecurity strategies. First, they invest in advanced cyber defense technologies such as threat detection systems and network monitoring tools.
Second, they train cybersecurity professionals to identify and respond to digital threats quickly. Additionally, many governments collaborate with private technology companies to strengthen digital security.
As a result, modern cybersecurity efforts involve both government institutions and private-sector organizations working together.
6. Could cyber warfare replace traditional military conflicts?
Although cyber warfare is becoming increasingly important, it is unlikely to completely replace traditional military operations. However, it is often used alongside conventional warfare strategies.
For instance, cyber attacks might disrupt communication networks before a military operation begins. Therefore, cyber warfare is best understood as an additional layer of modern conflict rather than a complete replacement for traditional warfare.
Further Thoughts: The Growing Importance of the Digital Battlefield
Looking ahead, the role of US-Iran cyber warfare will likely expand as technology continues to evolve. In fact, digital infrastructure has become so deeply integrated into everyday life that cyber attacks could potentially disrupt entire societies.
For instance, advancements in artificial intelligence, automation, and data analytics may significantly increase the speed and sophistication of cyber operations. As a result, future cyber attacks could become more complex and harder to detect.
At the same time, governments are also strengthening their cyber defense capabilities. Many countries are investing in AI-powered cybersecurity systems, threat intelligence platforms, and real-time monitoring technologies. Consequently, the global cyber battlefield is turning into a continuous technological competition.
Moreover, international cooperation will become increasingly important. Since cyber threats can cross borders instantly, countries may need to collaborate more closely in order to prevent large-scale digital crises.
Ultimately, the rise of cyber warfare highlights a critical reality: modern conflicts are no longer limited to physical battlefields. Instead, they increasingly take place within the digital systems that power our economies, communication networks, and national security structures.
Therefore, understanding cyber warfare is essential not only for governments and security experts but also for everyday internet users. After all, as our world becomes more connected, the protection of digital infrastructure will remain one of the most important challenges of the 21st century.
Conclusion: The Invisible War in Cyberspace
The rise of US-Iran cyber warfare illustrates how modern conflicts have expanded far beyond traditional battlefields. Today, cyber operations can influence global security, economic stability, and public perception without a single shot being fired.
From malware attacks and cyber espionage to information warfare and AI-powered cyber weapons, the digital battlefield has become an essential element of modern strategy.
Consequently, governments around the world are investing heavily in cybersecurity defenses and cyber warfare capabilities.
As technology continues to evolve, the importance of cyberspace in global conflicts will only grow. The next major battles between nations may not occur on land or in the sky but inside networks, data centers, and digital systems that power our world.